Monday, December 27, 2010
Secure Sockets Layer
A protocol developed by Netscape for transmitting private documents via the Internet.

Copyright
Is a set of exclusive rights granted by the law of a jurisdiction to the author or creator of an original work, including the right to copy, distribute and adapt the work.

boolean Logic
Is a complete system for logical operations, used in many systems. It was named after George Boole, who first defined an algebraic system of logic in the mid 19th century. Boolean logic has many applications in electronics, computer hardware and software, and is the basis of all modern digital electronics.

Blog
Website that allows users to reflect, share opinions, and discuss various topics in the form of an online journal while readers may comment on posts.

Wiki
Is a website that allows the easy creation and editing of any number of interlinked web pages via a web browser using a simplified markup language.

Website
Is a collection of related web pages, images, videos or other digital assets that are addressed relative to a common Uniform Resource Locator (URL), often consisting of only the domain name, or the IP address, and the root path in an Internet Protocol based network. A web site is hosted on at least one web server, accessible by a network such as the Internet or a private local area network.

Web 2.0
Is commonly associated with web applications that works around interactive systemic biases, interoperability, user centered design, and developing the World Wide Web.


Uniform Resource Locator (URL)
Is a (URI) that specifies where an identified resource is available and the mechanism for retrieving it.

Social Networking Site
Is an online service, platform, or site that focuses on building and reflecting of social networks or social relations among people.

Really Simple Syndication(RSS)
Formats used to publish frequently updated works such as blog entries, news headlines, audio, and video in a standardized format.

Portal
A Web portal or public portal refers to a Web site or service that offers a broad array of resources and services, such as e-mail, forums, and search engines.

Podcast
Is a series of digital media files (audio or video) that are released episodically and often downloaded through the web.

Internet Protocol (IP) Address
Is a numerical label assigned to each device participating in a computer network that uses the Internet Protocol for communication.

Hypertext Transfer Protocol (HTTP)
Is a networking protocol for distributed, collaborative, hypermedia information systems.

Domain
A set of common requirements, terminology, and functionality for any software program constructed to solve a problem in the area of computer programming.

Friday, December 17, 2010
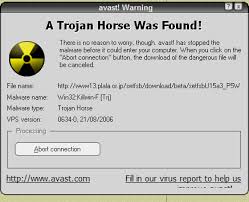
Trojan Horse
Is malware that appears to perform a desirable function for the user prior to run or install but instead unauthorized access of the user's computer system.
teleconferencing
Is the live exchange of information among several persons and machines remote from one another but linked by a telecommunications system.

Tagging
Is an argument to a subroutine that determines other arguments passed to it.
| AmigaOS 1.3 | AmigaOS 2.0+ |
|---|---|
struct Window *wnd; struct NewWindow nw = { 10, 10, 100, 100, 0, 1, IDCMP_CLOSEWINDOW, WFLG_SIZEGADGET | WFLG_DRAGBAR | WFLG_DEPTHGADGET | WFLG_CLOSEGADGET | WFLG_ACTIVATE, NULL, NULL, "WikiWindow", NULL, NULL, 0, 0, 640, 400, WBENCHSCREEN }; wnd = OpenWindow(&nw); | struct Window *wnd; wnd = OpenWindowTags(NULL, WA_Left, 10, WA_Top, 10, WA_Width, 100, WA_Height, 100, WA_IDCMP, IDCMP_CLOSEWINDOW, WA_Flags, WFLG_SIZEGADGET | WFLG_DRAGBAR | WFLG_DEPTHGADGET | WFLG_CLOSEGADGET | WFLG_ACTIVATE, WA_Title, "WikiWindow", WA_PubScreenName, "Workbench", TAG_DONE ); |
RDF Summary
A product to display content from other web sites provided they make it available in RSS 0.9, 0.91, 0.92 or RSS 1.0 format.

Pyramid Schemes
Scheming people into investing their "company", but really those people are robbing people of their money. Pyramid Schemes are illegal.

Phishing
The act of sending a email, to a person and falsely claim to be someone else so that person can steal you personal information.

Netiquette
Is a set of social conventions that interaction over networks, ranging from Usenet and mailing lists to blogs and forums.

Logic Bomb
A piece of code intentionally inserted into a software system that will set off a malicious function, means crashes a user computer.

Subscribe to:
Comments (Atom)

